# Enabling DNS over TLS on Fedora 42 with systemd-resolved
Recently, I have been exploring to encrypt my DNS traffic on Fedora 42 using DNS over TLS (DoT). Along the way, I ran into confusing symlinks, missing config files, and a few misconceptions about how Fedora handles DNS under the hood. Here's everything I learned, condensed into a practical guide for anyone else trying to harden their DNS on Linux.
---
## TL;DR
- Fedora uses `systemd-resolved` for DNS.
- `/etc/resolv.conf` is usually a **symlink** to a stub file—**don't edit it directly**.
- Use a drop-in config in `/etc/systemd/resolved.conf.d/` to enable DNS over TLS.
- DNS over HTTPS (DoH) is **not supported** by `systemd-resolved`.
- Cloudflare and Quad9 are good DNS providers with DoT support.
---
## What I Actually Did
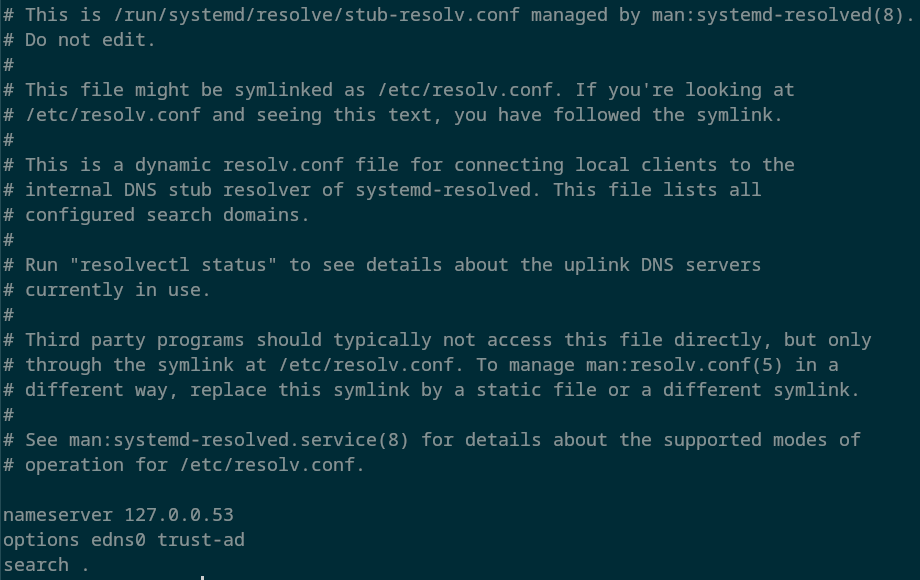
### 1. Discovered `/etc/resolv.conf` is a symlink
```
ls -l /etc/resolv.conf
```
Expected output:
```
/etc/resolv.conf -> ../run/systemd/resolve/stub-resolv.conf
```
This confirms `systemd-resolved` is managing DNS. Editing this file is useless—it’s managed dynamically:
---
### 2. Created a config directory for custom settings
```
sudo mkdir -p /etc/systemd/resolved.conf.d
```
Then created a new config file:
```
sudo nano /etc/systemd/resolved.conf.d/dns-over-tls.conf
```
---
### 3. Configured DNS Over TLS
In that file, I added:
```
[Resolve]DNS=1.1.1.1#cloudflare-dns.com 9.9.9.9#dns.quad9.netDNSOverTLS=yes
```
Here’s what this does:
- Sets two DoT-enabled resolvers (Cloudflare and Quad9).
- Enforces encrypted DNS transport via TLS.
---
### 4. Restarted systemd-resolved
```
sudo systemctl restart systemd-resolved
```
---
### 5. Verified DoT was working
```
resolvectl status
```
Look for:
```
DNS Over TLS: yes
```
🎉 Done!
---
## Why DNS over TLS (and not HTTPS)?
While both DNS over TLS (DoT) and DNS over HTTPS (DoH) encrypt DNS traffic to prevent snooping and tampering, there are key differences:
|Protocol|Port|Protocol|Common Clients|
|---|---|---|---|
|DoT|853|TLS|`systemd-resolved`, `stubby`|
|DoH|443|HTTPS|Browsers, `cloudflared`, `dnscrypt-proxy`|
We chose **DNS over TLS** for this setup because:
- **Fedora 42 with systemd-resolved only supports DoT** natively.
- DoT is simpler to configure at the system level (no extra proxies).
- DoT separates DNS from other HTTPS traffic, making it easier to monitor/debug.
If you need DoH, you'll have to install and run an external proxy like `cloudflared` or `dnscrypt-proxy`, which adds complexity. Since our goal was a clean, system-integrated solution using what's already available on Fedora 42, **DoT was the right fit.**
---
## What I Learned
- `systemd-resolved` is more powerful than I thought, but poorly documented in some areas.
- The real DNS config lives in `/etc/systemd/resolved.conf` or `resolved.conf.d/` drop-ins.
- The `/etc/resolv.conf` file is a stub and shouldn't be edited—it’s managed dynamically.
- DNS over TLS is natively supported. DNS over HTTPS is **not** (use `cloudflared` or `dnscrypt-proxy` for that).
---
## References
- [systemd-resolved Arch Wiki](https://wiki.archlinux.org/title/Systemd-resolved)
- [Fedora System Administrator’s Guide – Networking](https://docs.fedoraproject.org/en-US/fedora/latest/system-administrators-guide/networking/)
- [Cloudflare DNS-over-TLS docs](https://developers.cloudflare.com/1.1.1.1/encryption/dns-over-tls/)
- [Quad9 DNS security](https://www.quad9.net/)
---
## Optional Next Steps
- Use `cloudflared` or `dnscrypt-proxy` if you want DNS-over-HTTPS.
- Add monitoring with tools like Wireshark to verify encrypted DNS traffic.
- Use [DNS Leak Test](https://www.dnsleaktest.com/) to ensure nothing leaks to your ISP.
---
This was a quick little project that I embarked on, if you read this I hope this helped and that it saves you time!